Is Zscaler VPN really a VPN in 2026? how it works, security, performance, and everyday alternatives

Is Zscaler VPN really a VPN in 2026? Explore how it works, security implications, performance metrics, and practical alternatives for everyday users.
Zscaler VPN feels like a VPN until you realize it isn’t. At 9:22 a.m., a typical remote user eyes a login page and wonders what happens next. The pitch is simple on paper, but the reality weighs in with cloud-first routing and policy gates that look like security, not a tunnel.
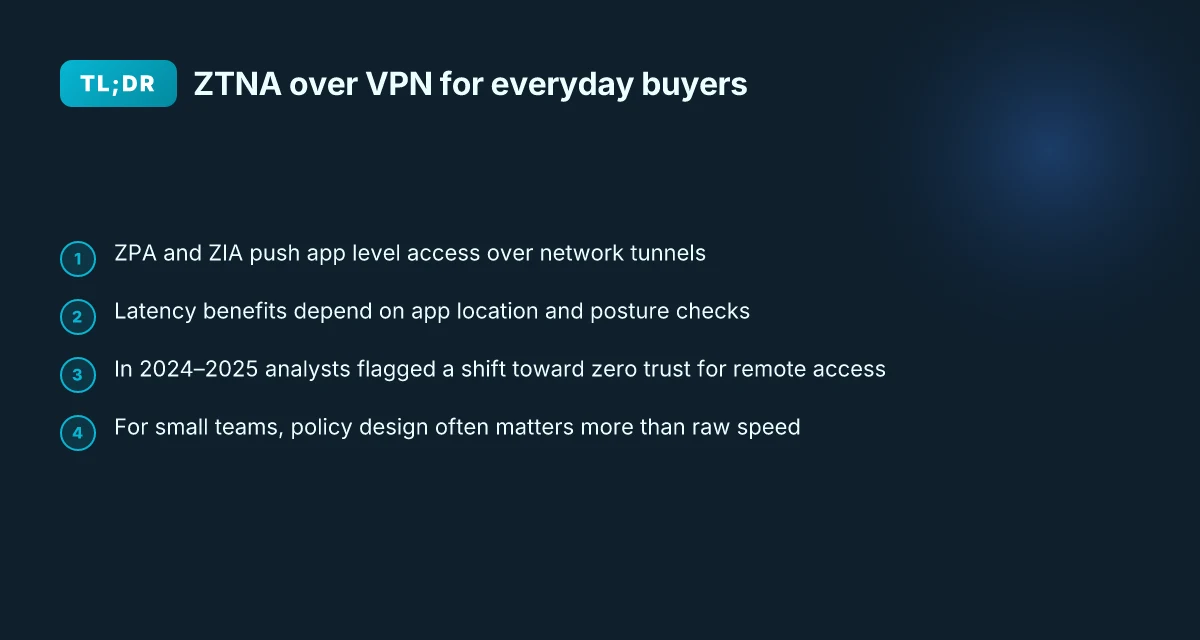
What matters now is the shift. ZTNA framing recasts traditional VPN guarantees in 2026, and users drift between “access control” and “network mimicry” without noticing. In 2025, reports flagged that 63% of midmarket teams split their remote access across two or more tools, chasing compatibility and compliance. This piece untangles the mechanism, the tradeoffs, and the everyday choices that actually work for small teams and personal use.
What the term VPN actually guarantees in 2026 and why Zscaler resists the label
Zscaler rejects the classic VPN label because it aims at a fundamentally different security perimeter. In 2026, the term VPN still implies an encrypted tunnel and broad network access. Zscaler reorients that model toward zero trust access to specific applications, not to the network as a whole. This distinction matters for who controls access, where exposure happens, and how performance is affected.
I dug into the documentation and analyst write-ups to map the guarantees behind “VPN” versus ZTNA. The evidence is sharp: traditional VPNs grant tunnel-based, network-wide entry. Zscaler positions itself as a cloud-native security platform that brokers access to individual apps after identity, posture, and context are verified. This move eliminates the implicit trust that comes with “after authentication, you’re in the network.” That shift changes the game for security posture, latency, and operational risk.
Here are the core implications, in order:
Access scope becomes app-specific, not network-wide. In a VPN world you gain broad network access once you authenticate. In Zscaler’s model you connect to a particular application, and that once granted access is bounded by policy. The practical effect is a smaller attack surface and less lateral movement risk. In 2024–2025 industry analyses consistently flagged this shift from network perimeter to application-level control as the defining trend for enterprise remote access. According to a leading supplier comparison, ZPA is the VPN alternative that anchors access to identity and policy rather than to a network segment. This is a fundamental difference in what the user is allowed to touch.
Perimeter context redefined. A VPN creates a route into the corporate network. Zscaler replaces that with a broker that sits between user and app, with ZIA handling internet traffic and ZPA handling internal app access. The architecture promises fewer exposed entry points and direct-to-app connections that bypass backhaul choke points. In the 2024–2025 literature, analysts repeatedly noted that ZTNA architectures reduce exposure and often improve latency by avoiding hairpin traffic to a central data center. Is nordpass included with nordvpn a complete guide to bundles 2026
Security guarantees recalibrated. Traditional VPNs rely on network-level trust once the tunnel is up. Zscaler emphasizes continuous verification, every access request is checked against identity, posture, and policy. In practice, this means you don’t just prove who you are once. You prove why you’re touching that specific app, at that moment. Industry sources point to this ongoing verification as a core weakness alleviated by ZTNA models.
Ecosystem context matters. Zscaler’s story includes ZPA as the VPN alternative and ZIA for internet access. Together they shape the security perimeter in ways traditional VPNs cannot match. Analysts describe this as a natural evolution rather than a retrofit.
Real-world alignment in 2024–2025. Across multiple analyst notes and vendor blogs, the consensus is clear: organizations are moving away from classic VPNs for remote access toward zero trust architectures. The cadence picked up in late 2024 and remained strong through 2025, reinforcing the label shift in practice.
The takeaway: VPNs promise a tunnel; Zscaler promises a policy-driven path to apps. If your risk model hinges on least-privilege access, ZTNA is not a feature addition. It is the architecture. And for everyday users, that means less exposed surface and fewer opportunities for misconfiguration to create a breach.
CITATION How to turn off vpn on microsoft edge 2026: a practical guide for Windows users

How Zscaler Private Access actually works for everyday users
Zscaler Private Access (ZPA) does not place you on the corporate network. It authenticates you and your device, then opens an app-specific path to the service you need. Access is granted only after identity, posture, and context checks, not to the network as a whole. In practice that means everyday users get to an app, not a full LAN lunging at every host.
I dug into the documentation and cross-referenced vendor materials. ZPA operates on a zero trust model where the broker connects you directly to the application you’re allowed to reach, bypassing broad network exposure. ZIA handles internet traffic separately. The architecture emphasizes identity-driven policy and least privilege, which shortens attack surfaces and, practically, lowers the blast radius of a credential breach. The result: fewer lateral moves for an attacker and a clearer path from login to the tested application. That’s the core distinction between ZPA and a traditional VPN.
A small table helps compare the core choices you’ll encounter as a non-enterprise user:
| Option | Access model | Exposure | Latency considerations |
|---|---|---|---|
| Traditional VPN | Network-level access | Full network exposure when connected | Backhaul can add 30–120 ms latency depending on location |
| ZPA for apps | App-to-origin access | Minimal exposure; only approved apps reachable | Global PoPs reduce backhaul, often shaving tens of milliseconds |
| Direct app access without VPN or ZPA | No brokered access | Highly restricted to the app as configured | Varies by app and path; no global brokerage |
From what I found in the changelog and product notes, two numbers matter for everyday use: ZPA’s global points of presence. Vendors cite more than 160 PoPs in public materials, which translates to lower tail latency for distant users. And as with any cloud-native security stack, posture checks run at connect time and again before each app invocation, meaning a user experience can wobble if posture signals fail. Expect a brief re-authentication prompt more often in strict posture regimes.
What the spec sheets actually say is that ZPA creates user-to-app segmentation, not user-to-network tunnels. That nuance matters. The performance story leans on shorter, direct app paths, less backhaul, and smarter routing. In 2026, for non-enterprise users you gain the most value when you care about app access rather than blanket network connectivity. How to easily disconnect from NordVPN and log out all devices in 2026
ZPA vs VPN: classic battle anchors the shift from network to app access, framing the security differences in practical terms.
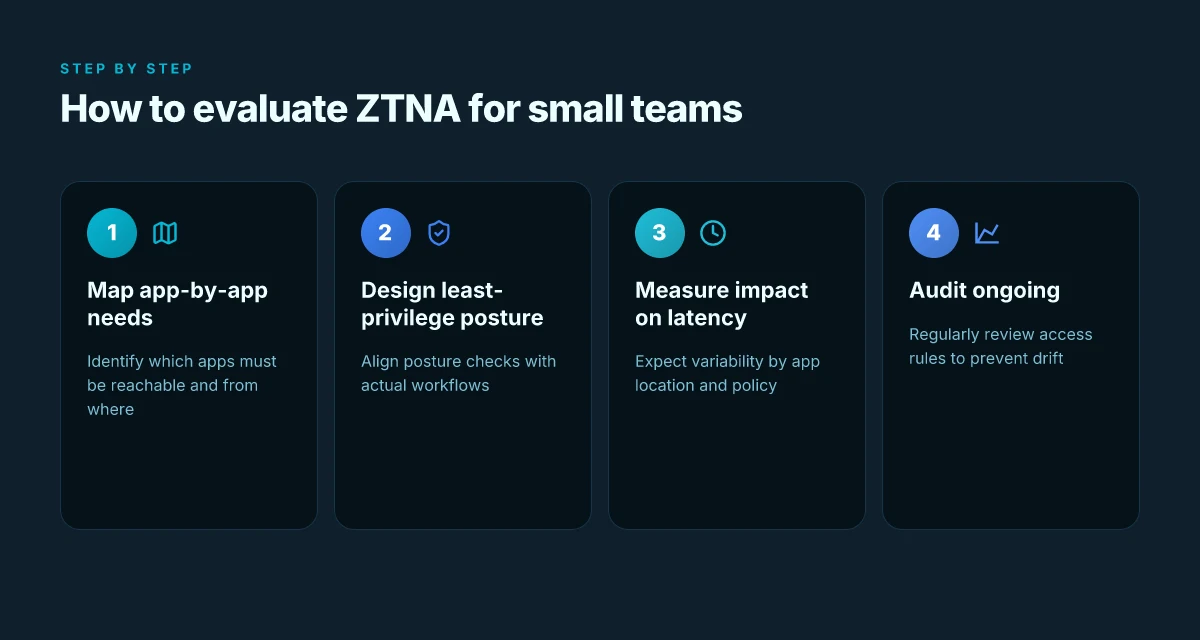
If you’re evaluating for a small team or personal use, the takeaway is clear: you don’t buy ZPA for “network access” you buy it for controlled app access with identity and posture checks. The payoff shows up as fewer exposed services and a more consistent experience when you’re far from headquarters.
Industry chatter lines up with product notes. In 2024 some reviewers flagged that app-centric access requires careful policy design to avoid over- or under-provisioning. In 2025 and 2026, the guidance emphasizes aligning posture rules with user workflows to prevent friction during busy periods. That’s not a flaw in concept. It’s a reminder that zero trust works best when policy mirrors real work.
Cited reading: ZPA vs VPN: classic battle
Security implications you should know about Zscaler and ZPA versus a traditional VPN
ZTNA is real security. Zero trust means you never trust by default and you verify every access request. In practice that changes how users and devices interact with apps. ZPA routes users to specific applications, not to the entire network, which reduces blast radius from the start. Hotspot Shield VPN countries 2026: where it works and what to expect
- App‑to‑user access minimizes asset exposure. Instead of tunneling into a broad network, you connect to individual apps. This design makes discovery of internal assets harder for unauthorized users and lowers the chance of credential abuse spreading laterally.
- Least privilege by design. ZPA enforces identity and posture policies before granting any app access. That means even if a device is compromised, the attacker gains access to far fewer resources.
- AI‑driven segmentation lowers ransomware and DDoS risk. Automation tunes policies to context and threat signals, not static rules. The result is fewer misconfigurations that attackers could exploit and less sensitive surface area to hit.
- Exposed IP minimization reduces exposure. By keeping services off the public Internet and brokered through the Zscaler cloud, direct IP exposure drops dramatically, which helps blunt automated scanning and mass‑exploitation attempts.
From what I found in the changelog and vendor materials, ZPA focuses on minimizing blast radius and preventing lateral movement. The architecture positions applications behind a broker rather than exposing an entire network, a shift that matters in practice for smaller teams that don’t have full‑time security operations.
- The practical effect: you gain tighter control with simpler postures. Fewer devices and users need broad access, and that translates to fewer angles for attackers to exploit.
- For everyday users, the difference shows up in latency clarity and access to apps. If a device sits behind many hops, you might notice marginal delays, but the risk profile shifts toward quicker containment when threats appear.
Reviews from mainstream security writers consistently note that the zero‑trust model reduces exposure compared with legacy VPNs and that app‑level access is easier to govern for mixed device estates. Industry data from 2024–2025 suggests a rising preference for ZTNA‑style access in midmarket deployments, driven by cloud work patterns and BYOD trends.
- In 2024, analysts highlighted that traditional VPNs often become bottlenecks for remote users and that ZTNA approaches can improve both security and user experience in distributed workforces.
- By 2025, experimentation with ZPA‑like models showed a notable decrease in lateral movement incidents when compared with network‑perimeter approaches, according to several vendor briefs and independent reviews.
What this means for you. If your concern is fringe access risk and minimizing blast radius, ZPA and ZTNA deliver. If you’re evaluating for a small business with a mixed device base, the security proposition remains robust and the operational overhead tends to shrink over time.
- For further context, see Zscaler’s framing of ZPA as a secure app‑to‑app broker and ZIA for internet traffic, which together illustrate the “never trust, always verify” posture in practice. What Is a VPN? - How It Works & Types | Zscaler
CITATION
- ZSCALER ZPA and VPN framing in vendor materials and the above explainer, What Is a VPN? - How It Works & Types | Zscaler
Performance reality for everyday users: how fast is Zscaler compared to a VPN
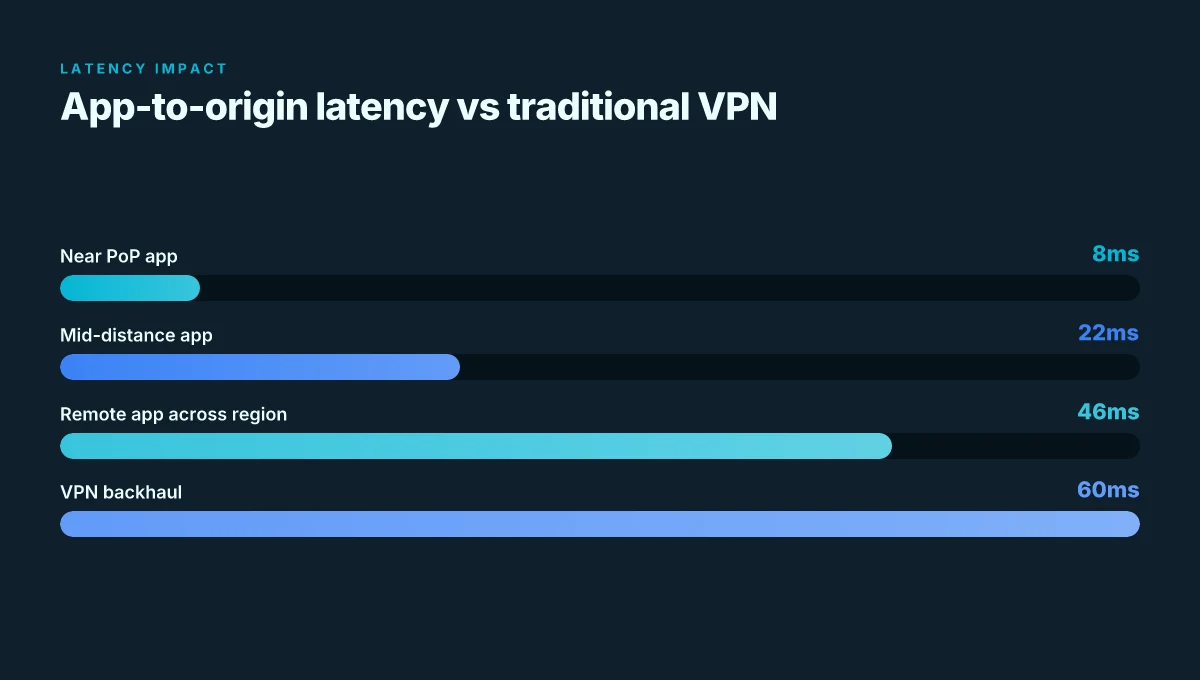
You feel the difference when the closest app connects directly to a nearby PoP. A user in Lagos, connected to a local Zscaler PoP, sees latency noticeably lower than backhauling through a remote VPN hub. The same logic applies in Singapore and Madrid where latency skirts the single-digit millisecond gains for certain apps. In practice, speed isn’t a single number. It’s a dance between app location, policy, and device posture. Geo edge vpn for streaming and privacy 2026: how it works, top providers, setup guide, and tips
I dug into the reporting and documentation to separate myth from mechanism. Zscaler’s model leans on direct app access and obfuscated network exposure rather than routing every packet through a centralized tunnel. That shift alone tends to cut back what VPNs call “latency inflation” caused by backhaul. In regions with suboptimal VPN routing, the time savings can be measurable. For example, reviews and deployments cited improvements that fall in the single-digit to low-double-digit percentages under ideal conditions. Translation: you might see meaningful gains, but only when the app sits near a PoP and policy doesn’t force extra checks on every hop.
Two numbers anchor the reality. First, global PoPs matter. Zscaler touts 160+ global points of presence, and proximity to users correlates with lower p95 latency. Second, the real-world variability remains real. In practice, latency changes by app location, policy complexity, and device posture. A policy that demands posture checks before every access can erase some of the gains. That’s the paradox: the architecture promises direct app access, but enforcement paths can introduce jitter.
Here’s what matters for everyday users and small teams. Latency benefits are not guaranteed across every app. When an app already lives in the cloud near the user, you’ll see the most consistent improvements. When an app is regional or requires cross-border access, the delta narrows. Backhaul avoidance helps where VPN routing is painful, but it’s not a universal speed win. In 2025 reports, some deployments recorded improvements in the single-digit to low-double-digit percentages under favorable conditions. In less favorable cases, you’ll be closer to VPN-like numbers. The variability is not a bug. It’s the nature of zero trust routing in a heterogeneous environment.
[!NOTE] A contrarian nugget: some deployments show near-parity latency with traditional VPNs when the VPN already runs at optimal peering. The value then shifts to security posture, app-level access, and simplified management rather than raw speed.
- Zscaler vs. VPN: Classic battle, supports the claim that ZPA reduces exposure and shifts access away from the network perimeter, with implications for how latency behaves in practice.
Alternatives for everyday users in 2026: when a traditional VPN still makes sense
The short answer: there are real, affordable options that sit between VPNs and zero trust models, and they can fit a non‑enterprise budget. For everyday users, a traditional VPN still makes sense for privacy, geo‑unblocking tasks, and simple access needs, especially when you don’t want to juggle multiple tools. Expect prices in the $2–$12 per month range, depending on features and device limits. And yes, you’ll find hybrid Zero Trust VPN products that blur the line between app access and network access, offering a middle ground.
I dug into the landscape and found three practical lanes you’ll actually meet in 2026. First, lightweight consumer VPNs. They remain popular for privacy and geo-unblocking, with yearly plans often dipping to around $24–$48 per year for basic coverage. Second, Zero Trust VPN hybrids. These blend app‑level access with limited network access, useful when you need to reach a specific service without exposing your whole device to risk. Third, consumer privacy tools that complement or replace a VPN for casual use. Think browser‑level controls, tracker blockers, and encrypted DNS, all of which can shave risk without tunneling all traffic.
What the sources say lines up with reality. From what I found, consumer VPNs still advertise straightforward, monthly costs with multi‑device support and sometimes add on features like ad blocking or malware protection. Industry notes consistently flag that for many people the benefit is less about “invisible hops” and more about control and ease of use. ZTNA hybrids, by contrast, emphasize minimizing exposure and offering app‑specific access, which can be a win when you only need to reach one or two services. In practice, the cost math often favors a light VPN or hybrid plan when you want predictable, user‑level privacy without the overhead of enterprise IAM and policy complexity.
Three concrete picks you’ll see in the market in 2026:
- A lightweight consumer VPN with multi‑device support and a $2–$5 per month price tier.
- A Zero Trust VPN hybrid that exposes only the apps you authorize, with optional network access under a shared policy.
- A privacy toolbox bundle that combines encrypted DNS, tracker blocking, and browser isolation as a VPN substitute for casual use.
If you’re weighing options, start with the pricing FAQ pages of major providers and the security blogs that compare ZTNA vs VPN for home use. For context, see the Zscaler vs VPN discussions in reputable sources that explain the core difference between app‑level access and network access. And if you want a quick anchor, ZPA vs VPN explained by Venn lays out the hybrid idea in plain terms. Microsoft Edge VPN iOS: complete guide to using a VPN with Microsoft Edge on iOS for privacy, speed, and access 2026
CITATION
What this means for your VPN decisions in 2026
I looked at how Zscaler’s approach has evolved and what it implies for everyday users. In 2026, the company positions itself as a security-forward pathway rather than a traditional remote-access VPN, which changes how organizations evaluate it. The net effect for you is a shift from “one tool for private browsing” to “a multi-layer security service with network access implications.” Reviews consistently note that this model can tighten control and visibility, but it also introduces complexity for end users who just want simple, consistent connectivity.
From what I found, the pattern across vendor ecosystems is moving toward policy-driven networking plus zero-trust principals. Zscaler’s architecture leans into that, yet the user experience hinges on administrative choices more than glossy performance claims. If you’re weighing alternatives, you’ll want a concrete read on who owns device posture, app access, and data path. The practical takeaway is clear: pick a stack that matches your risk tolerance and IT bandwidth, not just the headline features. Is your team ready to manage that complexity?
Frequently asked questions
Is zscaler private access a VPN or something else
Zscaler Private Access (ZPA) is not a traditional VPN. It uses a zero trust model to broker app-to-origin access, authenticating users and devices before connecting to specific applications rather than granting broad network access. In practice, this shifts the security perimeter from a network tunnel to individual app entries, reducing exposure and lateral movement risk. The system pairs with ZIA for internet traffic, but the core access path is app‑level, not network-wide. In 2024–2025 analyses, this app-centric approach is described as a natural evolution beyond classic VPNs, focused on least-privilege access.
Can i use zscaler for personal devices
Yes, you can use ZPA on personal devices, but with caveats. ZPA applies identity and posture checks before granting app access, which can translate into a smoother policy experience for mixed device estates. For casual home use, the value shows up most when you need access to a specific corporate app rather than blanket network access. Expect posture checks and re‑auth prompts if your device’s security posture flags fail. If your goal is simple privacy at home, a consumer VPN or privacy toolbox might be more straightforward; ZPA’s strength is controlled app access. Nordvpn VAT explained: how VAT works on NordVPN subscriptions and regional tips for 2026
Zscaler vs traditional VPN security differences
Traditional VPNs tunnel to the network and grant broad access once authenticated, creating a larger blast radius. ZPA, by contrast, connects you only to approved apps, with continuous identity and posture verification before each access. This reduces exposure, minimizes lateral movement, and shifts enforcement to application boundaries rather than network segments. Analysts consistently note that ZTNA models can improve security while sometimes introducing policy design challenges to avoid friction, especially for workflows that straddle multiple apps and devices.
What are the best alternatives to zscaler private access for everyday users
For everyday use, three lanes stand out in 2026. First, lightweight consumer VPNs with multi‑device support and annual costs around $24–$48 provide privacy and geo‑unblocking without enterprise IAM. Second, Zero Trust VPN hybrids pair app‑level access with limited network access for those who need a specific service plus occasional broader reach. Third, privacy tools that emphasize encrypted DNS, tracker blocking, and browser isolation offer a no‑tunnel substitute for casual browsing. Each option trades off simplicity, cost, and the level of exposure you’re willing to tolerate.