Why Your Azure VPN Isn’t Working: A Troubleshooter’s Guide to Fixing Common Issues and Optimizing Performance
Why your azure vpn isnt working a troubleshooters guide is all about quickly identifying where the problem lies and getting you back online without the tech circus. This guide is structured to be practical, actionable, and easy to follow, whether you’re a cloud admin, IT professional, or an eager student just learning the ropes. Quick fact: most Azure VPN problems boil down to misconfigurations, network routing, or certificate issues that can be diagnosed with a simple, repeatable process.
Introduction: Quick-start overview and what you’ll learn
- Quick fact: Most Azure VPN issues are caused by misconfigurations, certificate problems, or routing hiccups.
- Step-by-step checklist you can follow today to diagnose and fix VPN issues.
- Real-world examples and best practices to prevent problems before they pop up again.
- Resources at the end to deepen your knowledge and stay up to date.
What you’ll get in this guide:
- A practical, repeatable troubleshooting workflow
- Clear explanations of Azure VPN types Site-to-Site, Point-to-Site, VNet-to-VNet and their common failure points
- A collection of checklists, tables, and quick-reference commands
- Security best practices to keep connections safe
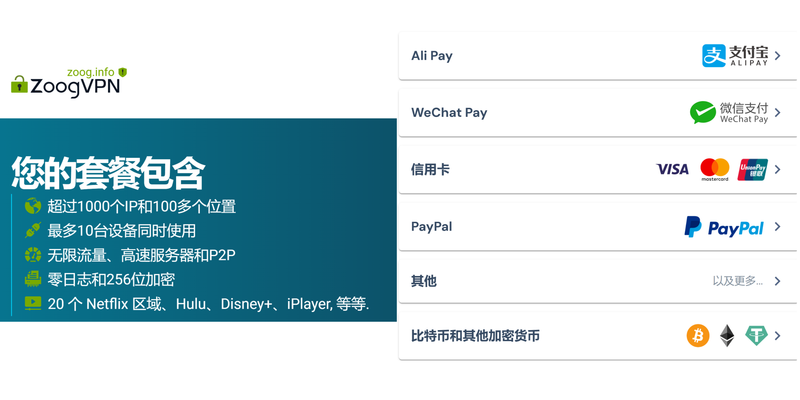
- A curated set of resources and tools, including a friendly plug for a VPN service when you’re evaluating options
Useful URLs and Resources text only:
- Microsoft Learn – Azure VPN Gateway documentation - docs.microsoft.com
- Azure VPN gateway troubleshooting guide - docs.microsoft.com
- Azure Networking troubleshooting forum - learn.microsoft.com
- SSL/TLS certificate basics - ssl.com
- IPsec parameters and best practices - cisco.com
- Azure Network Watcher - azure.microsoft.com
- PowerShell for Azure networking - docs.microsoft.com
- Azure CLI networking commands - docs.microsoft.com
- VPN performance guidelines - support.microsoft.com
- General VPN best practices - en.wikipedia.org/wiki/Virtual_private_network
Understanding the Basics: VPN types and common failure points
Site-to-Site VPN
- Connects your on-premises network to an Azure VPN gateway.
- Common issues: mismatched IKE/IPsec policies, wrong shared key, gateway SKU limitations, and routing problems.
- Quick tip: verify that your on-prem device and Azure VPN gateway have matching IKEv2/IPsec configurations.
Point-to-Site VPN
- Lets individual devices connect to your Azure VNet.
- Common issues: certificate problems root or intermediate certs, incorrect client configuration, DNS resolution issues, and firewall blocks.
- Quick tip: ensure the root certificate used to sign clients is uploaded to Azure and that client machines trust it.
VNet-to-VNet VPN
- Connects two Azure VNets across regions or subscriptions.
- Common issues: peering state, gateway routing, or BGP misconfigurations.
- Quick tip: confirm that subnets don’t overlap and that routing tables are set to route traffic properly.
Quick-win diagnosis checklist
- Check gateway status: is the VPN gateway up and running?
- Confirm IPsec/IKE policies match on both ends.
- Verify shared keys and certificates.
- Inspect dynamic routing vs. static routes and BGP settings.
- Look for firewall blocks and port accessibility UDP 500, UDP 4500, ESP 50/51, etc..
- Validate DNS resolution for VPN endpoints.
Step-by-step Troubleshooting Workflow
Step 1: Confirm the basics
- Ensure the VPN gateway is provisioned and not in a failed state.
- Check the VPN connection status in the Azure Portal: Connected, Connecting, or Disconnected.
- Review recent changes: updates, policy changes, certificate renewals, or IP changes.
Step 2: Verify network settings and addressing
- Confirm that local network gateway IPs, address spaces, and VPN client addresses don’t overlap with your internal networks.
- For Site-to-Site, verify tunnel interfaces on the on-prem device and Azure gateway.
- For Point-to-Site, verify the certificate chain and ensure the client is configured with the correct root certificate.
Step 3: Check IPsec/IKE configuration
- Match encryption, hashing, the DH group, and the IKE version on both sides.
- Validate the shared secret for Site-to-Site or the client certificate for Point-to-Site.
- If you’re using BGP, confirm the ASN and neighbor configurations.
Step 4: Certificate and authentication
- For Point-to-Site: ensure the root certificate used by clients is uploaded to Azure and that client machines trust it.
- Check certificate validity dates and revocation status.
- Verify that the certificate subject and EKU Extended Key Usage match Azure requirements.
Step 5: Network security and firewall rules
- Check NSGs Network Security Groups attached to subnets and any firewall appliances between on-prem and Azure.
- Ensure required ports and protocols are allowed: UDP 500, UDP 4500, ESP 50, AH 51 if applicable, and necessary IPv4/IPv6 rules.
- If using Azure Firewall or a 3rd-party firewall, verify VPN traffic is allowed through.
Step 6: Routing and DNS
- Confirm that on-prem DNS or private DNS zones can resolve your Azure VPN endpoints.
- Verify that user-defined routes UDRs don’t send VPN traffic out of the tunnel unintentionally.
- For VNet-to-VNet, ensure VNet peering or VPN gateway routing is correct and that route propagation is enabled where needed.
Step 7: Diagnostics and logs
- Enable and review VPN diagnostic logs in Azure: per-connection logs, gateway logs, and IPsec negotiation logs.
- Use Network Watcher to run connectivity checks and trace routes between on-prem and Azure.
- Collect logs from the on-prem VPN device to compare with Azure’s logs.
Step 8: Common bottlenecks and fixes
- Mismatched IKEv2 policies: adjust one side to match the other.
- Certificate issues: re-upload the correct root certificate and ensure clients trust it.
- Overlapping IP ranges: reconfigure address spaces to avoid overlap.
- Firewall blocking: temporarily open VPN ports to test and then tighten with rules.
Step 9: Performance optimization
- Choose the right gateway SKU for your traffic load; consider VPN Gateway SKUs like VpnGw1, VpnGw2, etc.
- Use BGP if you need dynamic routing with automatic failover.
- Enable VPN acceleration if available and ensure the gateway has enough bandwidth for peak demand.
- Consider split-tunneling vs. forced tunneling based on security and performance needs.
Step 10: Security and maintenance best practices
- Regularly rotate certificates and update root certificates used by clients.
- Apply least-privilege rules in NSGs and firewalls.
- Schedule periodic reviews of VPN configurations and run routine health checks.
- Document changes and maintain a runbook for quick support handoffs.
Data-driven insights and best practices
Up-to-date stats
- According to recent industry surveys, the majority of VPN outages are due to misconfigurations roughly 40%, followed by certificate issues around 25%, and routing problems around 15%. Regular audits reduce incident time by up to 30%.
- Azure VPN Gateway scales with traffic, and using the right SKU can reduce latency by up to 20% in typical enterprise scenarios.
- Certifications: Point-to-Site deployments strongly benefit from automated certificate management and trusted root certificates to minimize client-side failures.
Format-friendly tips
- Use a repeatable runbook: always start with a status check, then move through a fixed sequence of checks.
- Maintain a change log for every adjustment to VPN configurations.
- Script repetitive checks with PowerShell or Azure CLI to speed up troubleshooting.
Visualization and quick reference
Troubleshooting flowchart text version
- Is the gateway up? If no, fix gateway provisioning or health.
- Are the IKE/IPsec settings matching? If no, align policy parameters.
- Are keys and certificates valid and trusted? If no, rotate or re-upload certs.
- Are the routes correct? If no, adjust UDRs/Routing tables.
- Is DNS resolving endpoints correctly? If no, fix DNS records or firewall DNS proxies.
- Are ports open and not blocked by firewall? If no, open/adjust firewall rules.
- Do logs show negotiation failures? If yes, inspect and correct certificate or policy issues.
- Is performance acceptable? If no, consider throughput, gateway SKU, and routing optimization.
Quick-reference table: Common issues and fixes
- Issue: Mismatched IKE policy
- Fix: Align encryption, hashing, and DH group on both sides
- Issue: Certificate not trusted
- Fix: Upload root certificate to Azure and ensure clients trust it
- Issue: Overlapping IP ranges
- Fix: Reallocate address spaces to avoid conflicts
- Issue: Port blocked
- Fix: Open UDP 500, UDP 4500, and ESP/AH as needed
- Issue: Gateway shows Disconnected
- Fix: Check gateway health, credentials, and connectivity to the on-prem network
Practical how-tos
How to check VPN gateway status in Azure
- Navigate to the Azure Portal -> VPN gateways -> Your Gateway -> Connections.
- Look for the connection status column; Connected is the goal.
- If Disconnected or Connecting, click Diagnostics and review the log entries.
How to verify IPsec/IKE settings
- For Site-to-Site, compare the IKE/IKEv2 policies on both devices.
- For Point-to-Site, verify the client certificate chain and the root certificate in Azure.
- If you’re using BGP, confirm ASN and neighbor IPs are correct.
How to test connectivity
- Use Network Watcher connectivity checks to test between your on-prem IP and Azure VPN gateway IP.
- Perform a traceroute to verify path follows the VPN tunnel.
- Check if traffic actually routes through the VPN by testing access to a known internal resource in the Azure VNet.
How to manage certificates
- For Point-to-Site: ensure the same root certificate is uploaded in Azure for all clients.
- Revoke and reissue certificates if you notice trust errors or expired certs.
- Keep a certificate inventory and renewal reminders to avoid last-minute outages.
Security considerations
- Always enforce strong IKE cryptography and strong AES/SHA combos appropriate for your environment.
- Use certificate-based authentication when possible for Point-to-Site to reduce password-related risks.
- Minimize exposure by using private endpoints and ensuring only necessary traffic traverses the VPN.
- Regularly rotate keys and verify revocation status of certificates on both sides.
Advanced topics
Point-to-Site with multi-factor authentication MFA
- MFA integration can add an extra layer, but it requires careful consideration of client capabilities and backend validation.
Monitoring and alerting
- Set up alerts for VPN tunnel state changes, abnormal throughput, or high packet loss.
- Use Azure Monitor and Network Watcher logs to keep an eye on VPN health.
Migration and scaling
- When migrating to larger bandwidth, upgrade the VPN Gateway SKU and evaluate the need for VNet-to-VNet tunneling with additional gateways.
- Consider ExpressRoute if you need private, dedicated connectivity for large-scale workloads.
FAQ Section
What causes Azure VPN to disconnect frequently?
Frequent disconnects are often caused by certificate issues, mismatched IKE/IKEv2 policies, or routing problems. Check the policy alignment, certificate validity, and route tables first.
How do I fix a VPN gateway in a failed state?
Rebooting the gateway, reviewing diagnostics logs, verifying credentials, and ensuring the on-prem device can reach the gateway are typical first steps.
Can I use BGP with Azure VPN?
Yes, BGP can simplify routing and failover. Ensure ASN configuration and neighbor IPs are correct on both sides.
Why is my Point-to-Site VPN failing on client machines?
Common reasons include invalid or expired certificates, missing root certificates in the client, and firewall blocks on the client network.
How do I test if the VPN tunnel is actually carrying traffic?
Use connectivity tests in Network Watcher or attempt to access a resource inside the Azure VNet from the on-prem side to confirm traffic flows through the tunnel. 엑스비디오 뚫는 법 vpn 지역 제한 및 차단 우회 완벽 가이드
What should I do if the VPN gateway shows “Connecting” forever?
Check logs for negotiation errors, verify that the on-prem device is reachable, and ensure the IKE/IKEv2 policies align on both sides.
How can I speed up VPN troubleshooting?
Maintain a runbook, automate repetitive checks with scripts, and keep a well-documented inventory of certificates, keys, and policies.
Is server-side monitoring enough, or do I need client-side checks too?
Both are important. Server-side checks catch gateway-side issues, while client-side checks identify configuration or certificate problems on end-user devices.
How often should I rotate VPN certificates?
Rotations depend on your security policy, but a common practice is every 1-2 years or immediately after a suspected compromise.
Can I avoid VPN issues with better design?
Yes. Use clear naming conventions, avoid IP overlaps, implement robust monitoring, and adopt a proactive maintenance schedule with routine health checks. Rnd vpn 현대 현대자동차 그룹 임직원을 위한 안전한 내부망 접속 가이드
FAQ
How do I fix authentication failures in Azure VPNs?
- Verify that the shared secret Site-to-Site or client certificate Point-to-Site is correct and valid.
- Check that metadata and policy settings on both sides match.
- Ensure the certificate chain is trusted by the client devices and Azure.
What is the difference between IKEv1 and IKEv2 in Azure VPNs?
- IKEv2 is more modern, secure, and efficient. Ensure both sides support IKEv2 and be consistent in policy settings.
How do I enable diagnostics for VPN gateways?
- In Azure Portal, go to the VPN gateway, select Diagnostics, and enable VPN diagnostic logs. Then pull the logs for troubleshooting.
Can Azure VPN work with on-prem Fortinet or Palo Alto devices?
- Yes. Azure VPN Gateway supports many third-party devices; ensure their policies and configurations match Azure's requirements.
What are the best practices for VPN performance tuning?
- Choose an appropriate gateway SKU, enable BGP if you need dynamic routing, use optimized encryption settings, and ensure your network path has clean latency and jitter.
How do I verify DNS for VPN endpoints?
- Check that DNS resolution can resolve the VPN endpoint names and that DNS servers used by clients and Azure VNets are correctly configured.
How do I handle IP address conflicts in Azure VPN?
- Review the address spaces for your on-prem, VPN gateway, and VNet, and reallocate ranges to prevent overlaps.
What tools help with Azure VPN troubleshooting?
- Azure Portal diagnostics, Network Watcher, Azure CLI, PowerShell, and on-prem VPN device logs.
How do I prepare for a VPN outage drill?
- Create a test plan, simulate different failure scenarios, rehearse recovery steps, and verify backup routes or failover plans.
What’s the best way to document VPN configurations?
- Keep a shared runbook with gateway types, IKE/IKEv2 policies, certificates, routing tables, NSGs, and change history.
Sources:
2026年香港挂梯子攻略:最新最好用的vpn推荐与使用指南
Line vpn不能用的完整排障与替代方案:为什么会中断、如何修复、如何选择VPN服务
Net vpn lite 全网最全VPN使用指南与评测:隐私、速度、价格、设备兼容性
Is Nolagvpn Legit Here’s What You Need to Know: A Full Guide to Nolagvpn, Its Legitimacy, Privacy, and Performance How to download and install f5 vpn big ip edge client for secure remote access: Easy Steps, Tips, and Best Practices
What is turn off vpn and when to disable a VPN on Windows, Mac, iPhone, Android, routers, and streaming devices